|
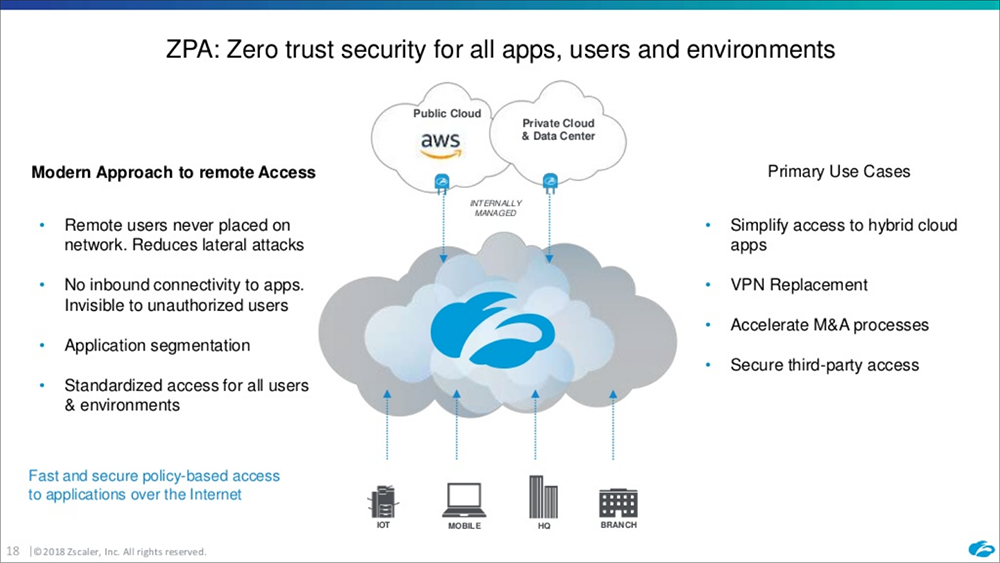
by Stuart Hardy, MD of zafrica In the past few weeks we’ve seen a spate of DDoS attacks against prominent service providers and enterprise companies, bringing the awareness of unnecessary network exposure into the spotlight once again. Given these attacks can and will increase in time, limiting the attack surface for any organisation has now become a top priority. A zero trust security framework is designed to combat these threats. Now there is little doubt to the transformative benefits of utilising Cloud for business application delivery. But, while the strategy to drive application delivery to the Cloud is well underway, by doing so, a lot of companies are inadvertently increasing the attack surface of their network. When connecting networks to private Cloud IaaS, it necessitates publishing IP addresses to expose the network and build network connections using IP Sec. Unfortunately by doing this; these addresses reveal the network to the world, creating easy targets for hackers who constantly look for vulnerabilities in networks, as is the recent case for the City of Joburg. What is Zero Trust? Essentially, zero trust centres on strong user identity, device health verification, validation of application health, and secure, least-privilege access to corporate resources and services. Read how Microsoft has implemented a Zero Trust security model. There is at least one company delivering a zero trust application access framework that eliminates the attack surface for organisations - and that’s Zscaler. They do this by making all applications and network connections dark for DC and public/private cloud access utilising Zscaler Private Access (ZPA). Basically, ZPA takes into consideration every requirement to deliver a secure network architecture related to modern challenges in growing mobility and cloud application delivery. Think of it as a modern-day version of an old age process (remote VPN, NNI). What are the benefits of implementing ZPA’s zero trust network:
Zscaler Private Access (ZPA) makes redundant a wide range of network devices and solutions (remote VPN, IP Sec, NNI, B2B, and Partner access), while improving security, user and application visibility and performance. For more information contact Stuart Hardy.
0 Comments
Leave a Reply. |
Value Added Distributor in sub-Saharan Africa
|
South Africa Contact: +27 11 568 9209
|
Mauritius Contact (USD): +230 5733 4955
|
|
Email: [email protected]
Unit 6, 64 Wessel Rd, Rivonia, Johannesburg, 2128
|
Office 2, Level 4, IconEbene, Lot B441, Rue de L’Institut, Ebene 72201 Mauritius
|
© COPYRIGHT 2019. ALL RIGHTS RESERVED.